Implementation of HTTP requests Google and YouTube after installing v2ray in CentOS 7.x of Alibaba Cloud Continental ECS
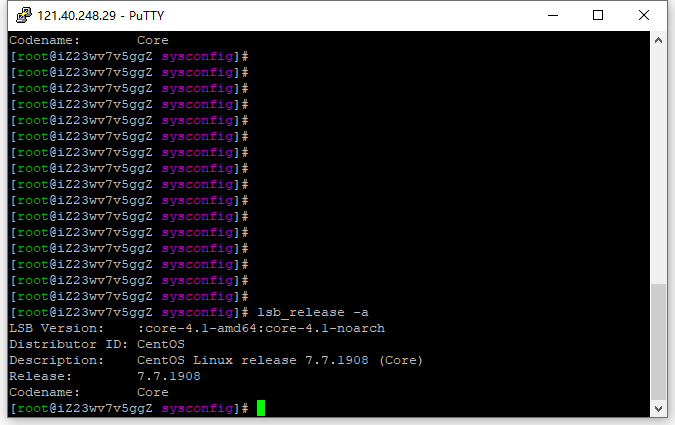
1. List all version information and execute the command: lsb_release -a. Version: CentOS 7.7. as shown in Figure 1
[root@iZ23wv7v5ggZ ~]# lsb_release -a LSB version: :core-4.1-amd64:core-4.1-noarch Distributor ID: CentOS Description: CentOS Linux Release 7.7.1908 (core) Release: 7.7.1908 codename: core [root@iZ23wv7v5ggZ ~]#
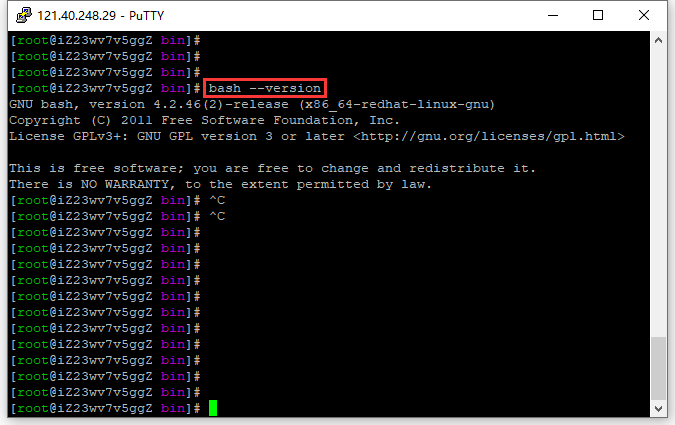
2. Check the bash version: 4.2.46. as shown in Figure 2
[root@iZ23wv7v5ggZ bin]# bash --version GNU Bash, Version 4.2.46(2)-release (x86_64-redhat-linux-gnu) Copyright (C) 2011 Free Software Foundation, Inc. license GPLv3+: GNU GPL version 3 or later <http://gnu.org/licenses/gpl.html> This is free software; you are free to change and redistribute it. There is no warranty, to the extent permitted by law. [root@iZ23wv7v5ggZ bin]# ^c [root@iZ23wv7v5ggZ bin]#
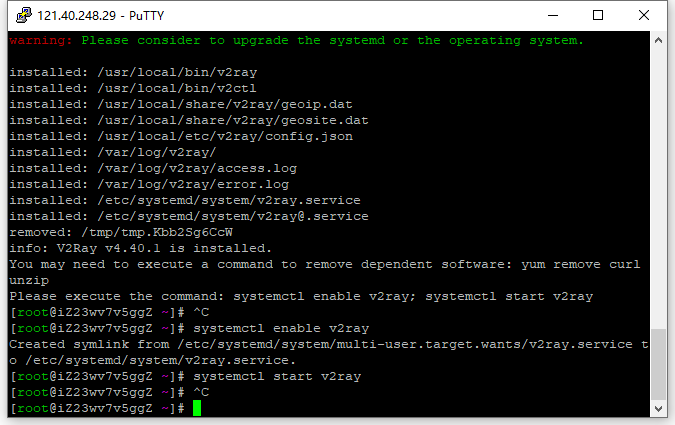
3. Install and update V2ray, refer to the website: https://github.com/v2fly/fhs-install-v2ray/blob/master/readme.zh-hans-cn.md . as shown in Figure 3
[root@iZ23wv7v5ggZ ~]# bash <(curl -l https://raw.githubusercontent.com/v2fly/fhs-install-v2ray/master/install-release.sh) % total % received % xferd average speed time time time current Dload Upload Total Spent Left Speed 100 21613 100 21613 0 0 21964 0 --:--:-- --:---------:--- 21964 Info: Installing v2ray v4.40.1 for x86_64 Downloading v2ray Archive: https://github.com/v2fly/v2ray-core/releases/download/v4.40.1/v2ray-linux-64.zip % total % received % xferd average speed time time time current Dload Upload Total Spent Left Speed 100 626 100 626 0 0 734 0 --:--:----------------------------------------------------------------- 100 12.3m 100 12.3m 0 0 2996k 0 0:00:04 0:00:04 --:--:--- 4167k Downloading verification file for v2ray archive: https://github.com/v2fly/v2ray-core/releases/download/v4.40.1/v2ray-linux-64.zip.dgst Info: extract the v2ray package to /tmp/tmp.kbb2sg6ccw and prepare it for installation. rm: cannot remove '/etc/systemd/system/v2ray.service.d/10-donot_touch_multi_conf': no such file or directory rm: cannot remove '/etc/systemd/system/v2ray@.service.d/10-donot_touch_multi_conf': no such file or directory Info: systemd service files have been installed successfully! Warning: the following are the actual parameters for the v2ray service startup. Warning: Please make sure the configuration file path is correctly set. ~~~~~~~~~~~~~~~~ [Unit] description=v2ray service documentation=https://www.v2fly.org/ after=network.target nss-lookup.target [Service] user=nobody CapabilityBoundingSet=CAP_NET_ADMIN CAP_NET_BIND_SERVICE AmbientCapabilities=CAP_NET_ADMIN CAP_NET_BIND_SERVICE nonewprivileges=true execstart=/usr/local/bin/v2ray -config /usr/local/etc/v2ray/config.json restart=on-failure RestartPreventExitStatus=23 [Install] WantedBy=Multi-User.Target # in case you have a good reason to do so, duplicate this file in the same directory and make your customizes there. # or all changes you made will be lost! # refer: https://www.freedesktop.org/software/systemd/man/systemd.unit.html [Service] execStart= execstart=/usr/local/bin/v2ray -config /usr/local/etc/v2ray/config.json ~~~~~~~~~~~~~~~~ Warning: the systemd version on the current operating system is too low. Warning: Please consider the systemd or the operating system. Installed: /usr/local/bin/v2ray Installed: /usr/local/bin/v2ctl Installed: /usr/local/share/v2ray/geoip.dat Installed: /usr/local/share/v2ray/geosite.dat Installed: /usr/local/etc/v2ray/config.json Installed: /var/log/v2ray/ Installed: /var/log/v2ray/access.log Installed: /var/log/v2ray/error.log Installed: /etc/systemd/system/v2ray.service Installed: /etc/systemd/system/v2ray@.service Removed: /tmp/tmp.kbb2sg6ccw Info: v2ray v4.40.1 is installed. You may need to execute a command to remove dependency software: yum remove curl unzip Please execute the command: systemctl enable v2ray; systemctl start v2ray [root@iZ23wv7v5ggZ ~]# systemctl enable v2ray created symlink from /etc/systemd/system/multi-user.target.wants/v2ray.service to /etc/systemd/system/v2ray.service. [root@iZ23wv7v5ggZ ~]# systemctl start v2ray [root@iZ23wv7v5ggZ ~]#
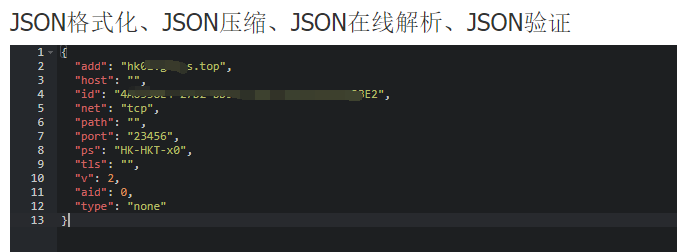
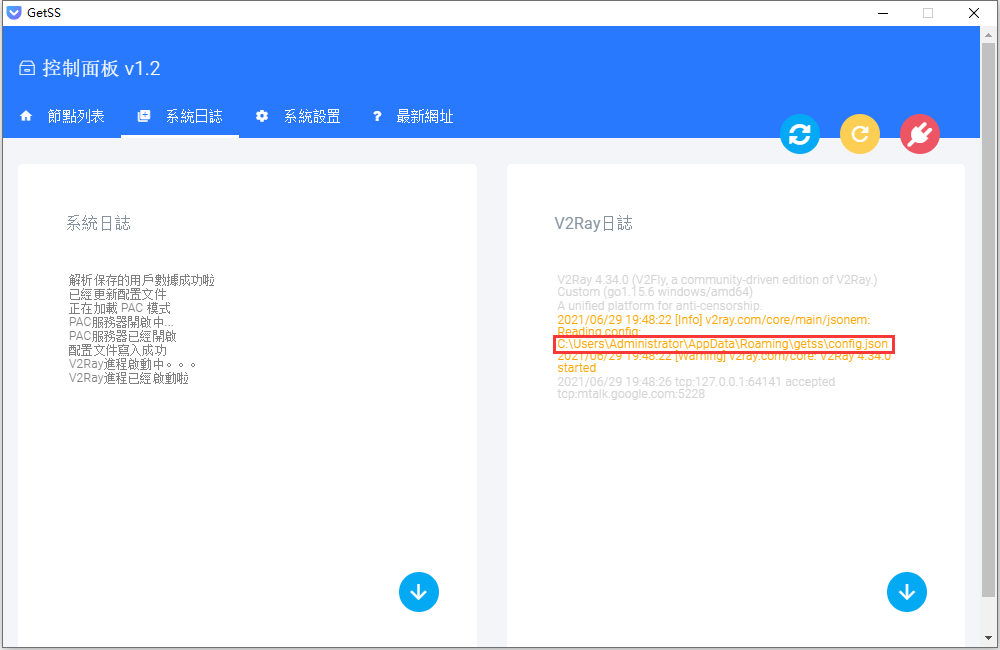
4. I purchased a commercial version of the V2ray server getss, select the Azure server in Hong Kong, and copy the URL. Its value is no longer available, I made changes. as shown in Figure 4
vmesss://eyjhzgqioijoazaxlmdldhnzlnrvccisimhvc3qioiiilcjpzci 6ijrbnjmzoeu0lti3rditqkq5my01mui1luizqjixruewm0jfmisim5ldci 6inrjccisinbhdggioiiiilcjwb3j0ijoimjm0ntyilcj5wcyi6ikhlluhlvc 14MCISINRScy66i6iiSinyIOJISIMFPZCI6MCWIDHLWZSI6IM5VBMuIFQ==
5. After decoding the value after vmess:// base64. JSON format, its value is as follows. Subsequently used to configure the V2RAY client on the Alibaba Cloud server. Its value is no longer available, I made changes. as shown in Figure 5
{
"add": "hk01.getss.top",
"host": "",
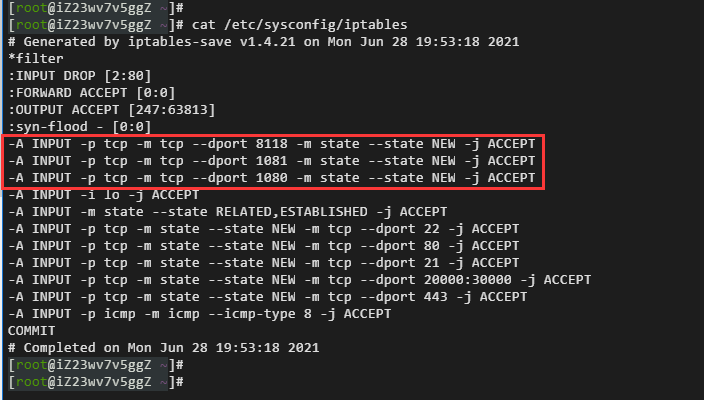
"id": "4a6338e4-27d2-bd93-515b5-b3b21ea6603be2",
"net": "tcp",
"path": "",
"port": "23456",
"ps": "hk-hkt-x0",
"tls": "",
"v": 2,
"aid": 0,
"type": "none"
}
6. Check the file /usr/local/etc/v2ray/config.json, its value is empty object
[root@iZ23wv7v5ggZ ~]# cat /usr/local/etc/v2ray/config.json
{}
[root@iZ23wv7v5ggZ ~]#
7. V2ray does not use the C/S (ie, client/server) structure of conventional proxy software, it can be used as a server or a client. Configure the client, refer to the file: C:\Users\Administrator\AppData\Roaming\Getss\Config.json. GETSS is a Windows client. Edit /usr/local/etc/v2ray/config.json. as shown in Figure 6
{
"policy": {
"levels": {
"0": {
"uplinkonly": 0
}
}
},
"inbound": {
"listen": "127.0.0.1",
"port": 1081,
"protocol": "socks",
"settings": {
"auth": "noauth",
"UDP": False,
"ip": "127.0.0.1"
}
},
"inbounddetour":[
{
"listen": "127.0.0.1",
"allocate": {
"strategy": "always",
"refresh": 5,
"concurrency": 3
},
"port": 8001,
"protocol": "http",
"tag": "httpdetour",
"domainoverride": [
"http",
"tls"
]#ATFP_CLOSE_Translate_span#,
"streamsettings": {},
"settings": {
"timeout": 0
}
}
],
"log": {
"loglevel": "warning"
},
"dns": {
"servers":[
"223.5.5.5"
]#ATFP_CLOSE_Translate_span#
},
"outbounddetour":[
{
"protocol": "freedom",
"tag": "direct",
"settings": {}
}
]#ATFP_CLOSE_Translate_span#,
"outbound": {
"sendthrough": "0.0.0.0",
"mux": {
"enabled": false,
"concurrency": 8
},
"protocol": "vmess",
"settings": {
"vnext":[
{
"address": "hk01.getss.top",
"port": 23456,
"users": [
{
"id": "4a6338e4-27d2-bd5593-51b5-b3b21ea03be2",
"alterid": 0,
"security": "auto",
"level": 0
}
]#ATFP_CLOSE_Translate_span#,
"remark": "hk-hkt-x0"
}
]
},
"streamsettings": {
"wssettings": {
"path": "",
"headers": {
"host": ""
}
},
"tcpsettings": {
"header": {
"type": "none"
}
},
"security": "",
"tlssettings": {
"servername": "",
"allowsecure": False
},
"httpSettings": {
"path": "",
"host":[
""
]#ATFP_CLOSE_Translate_span#
},
"kcpsettings": {
"header": {
"type": "none"
},
"mtu": 1350,
"congestion": false,
"tti": 20,
"uplinkcapacity": 5,
"writeBufferSize": 1,
"readBufferSize": 1,
"downlinkcapacity": 20
},
"network": "tcp"
}
}
}
8. Use the configuration check function (test option) provided by v2ray, because you can check the problems outside the json syntax error, such as sudden hand shaking and writing vmsss as vmss, and it is checked out at once. If it is a configuration file, this is the case.
[root@iZ23wv7v5ggZ ~]# /usr/local/bin/v2ray -test -config /usr/local/etc/v2ray/config.json V2Ray 4.40.1 (V2Fly, a Community-Driven Edition of V2ray.) Custom (Go1.16.5 Linux/AMD64) A unified platform for anti-censorship. configuration OK. [root@iZ23wv7v5ggZ ~]#
9. The authentication of the vMess protocol is based on time, and it must be ensured that the system time difference between the server and the client is within 90 seconds. Check the system time of Alibaba Cloud server.
[root@iZ23wv7v5ggZ ~]# date Thu Jun 24 16:50:13 CST 2021 [root@iZ23wv7v5ggZ ~]#
10. Actually the flow direction of the packet: {browser} <–(socks)–> {v2ray client inbound <–> v2ray client outbound} <–(vmess)–> {target website}.
11. View the ports linked to the proxy port 1081. Displays the Sockets in all connections.
[root@iZ23wv7v5ggZ ~]# netstat -nat | grep 1081 -a TCP6 0 0 :::1080 :::* listen [root@iZ23wv7v5ggZ ~]#
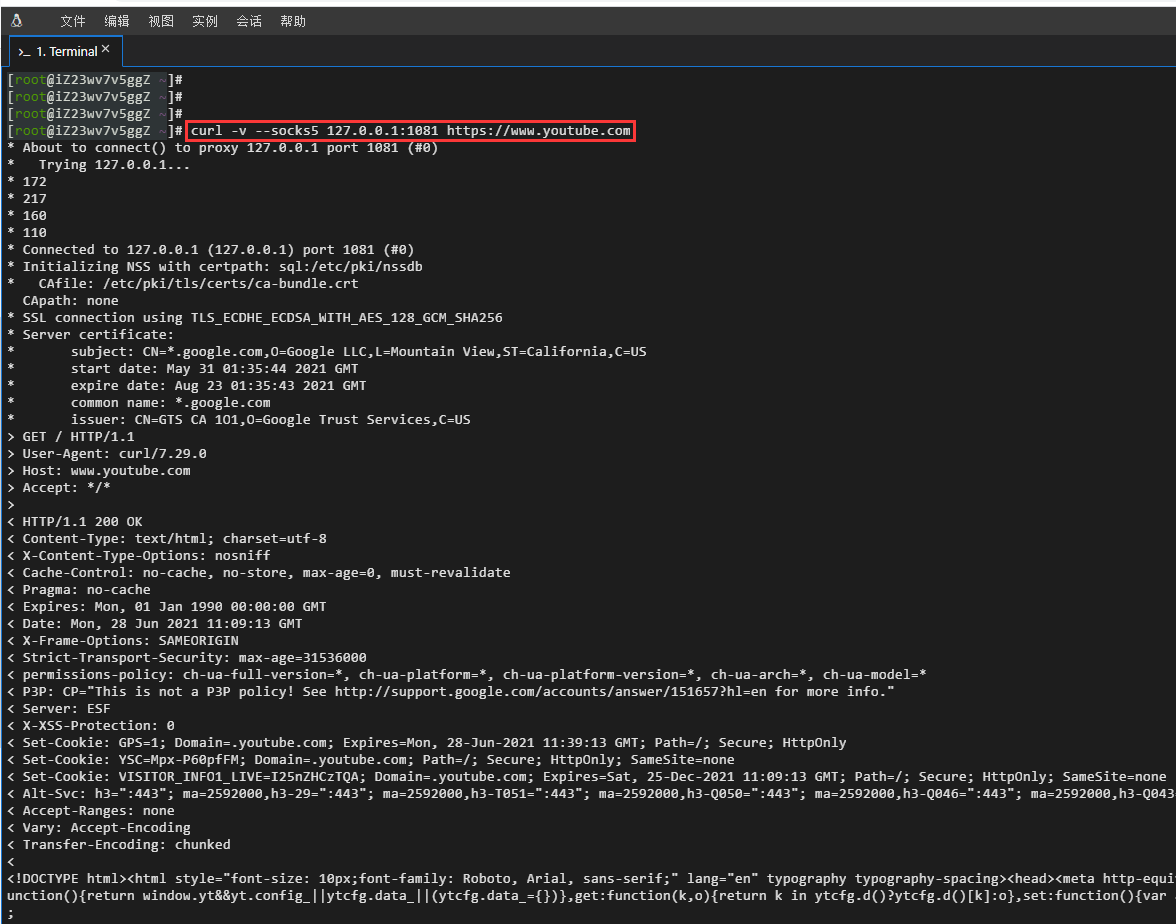
12. Test the Alibaba Cloud server-based SOCKS request http://httpbin.org/ip, https://www.google.com, https://www.youtube.com. The connection was successful. as shown in Figure 7
[root@iZ23wv7v5ggZ v2ray]# curl --socks5 127.0.0.1:1081 http://httpbin.org/IP
{
"origin": "14.192.49.13"
}
[root@iZ23wv7v5ggZ v2ray]# curl --socks5 127.0.0.1:1081 http://www.google.com
CURL: (52) Empty reply from server
[root@iZ23wv7v5ggZ v2ray]# curl --socks5 127.0.0.1:1081 https://www.google.com
Curl: (51) Unable to communicate securely with peer: requested domain name does not match the servers certificate.
[root@iZ23wv7v5ggZ v2ray]# curl -v --socks5 127.0.0.1:1081 https://sitekit.withgoogle.com
* about to connect() to proxy 127.0.0.1 port 1081 (#0)
* Trying 127.0.0.1...
* 216
* 58
* 200
* 49
* Connected to 127.0.0.1 (127.0.0.1) Port 1081 (#0)
*Initializing NSS with CertPath: SQL:/etc/pki/NSSDB
* cafile: /etc/pki/tls/certs/ca-bundle.crt
Capath: None
* SSL connection using TLS_ECDHE_ECDSA_With_AES_128_GCM_SHA256
* Server Certificate:
* Subject: cn=*.appspot.com,o=Google llc,l=mountain view,st=california,c=us
* Start Date: May 31 01:07:40 2021 GMT
* Expire Date: Aug 23 01:07:39 2021 GMT
* Common name: *.appspot.com
* issuer: cn=gts ca 1o1,o=google trust services, c=us
> get/http/1.1
> user-agent: curl/7.29.0
> host: sitekit.withgoogle.com
> accept: */*
>
< http/1.1 200 OK
< content-type: text/html; charset=utf-8
< vary: accept-encoding
< x-cloud-trace-context: f0ad2afe1e1a7fd9d592b1b2e4c62
<date: Fri, 25 Jun 2021 09:35:19 GMT
< server: Google Frontend
< content-length: 89089
< alt-svc: h3=":443"; ma=2592000,h3-29=":443"; ma=2592000,h3-t051=":443"; MA=2592000,H3-Q050=":443"; ma=2592000, H3-Q046=":443"; ma=2592000,h3-q043=":443"; ma=2592000, quic=":443"; ma=2592000; v="46,43"
<
<!doctype html>
[root@iZ23wv7v5ggZ ~]# curl -v --socks5 127.0.0.1:1081 https://www.youtube.com
* about to connect() to proxy 127.0.0.1 port 1081 (#0)
* Trying 127.0.0.1...
* 172
* 217
* 160
* 110
* Connected to 127.0.0.1 (127.0.0.1) Port 1081 (#0)
*Initializing NSS with CertPath: SQL:/etc/pki/NSSDB
* cafile: /etc/pki/tls/certs/ca-bundle.crt
Capath: None
* SSL connection using TLS_ECDHE_ECDSA_With_AES_128_GCM_SHA256
* Server Certificate:
* subject: cn=*.google.com,o=google llc,l=mountain view,st=california,c=us
* Start Date: May 31 01:35:44 2021 GMT
* Expire Date: Aug 23 01:35:43 2021 GMT
* Common name: *.google.com
* issuer: cn=gts ca 1o1,o=google trust services, c=us
> get/http/1.1
> user-agent: curl/7.29.0
> host: www.youtube.com
> accept: */*
>
< http/1.1 200 OK
< content-type: text/html; charset=utf-8
< x-content-type-options: nosniff
< cache-control: no-cache, no-store, max-age=0, must-revalidate
< pragma: no-cache
< Expires: Mon, 01 Jan 1990 00:00:00 GMT
< date: Mon, 28 Jun 2021 11:09:13 GMT
< x-frame-options: SameOrigin
< strict-transport-security: max-age=31536000
< permissions-policy: ch-ua-full-version=*, ch-ua-platform=*, ch-ua-platform-version=*, ch-ua-arch=*, ch-ua-model=*
< p3p: cp="this is not a p3p policy! see http://support.google.com/accounts/answer/151657?hl=en for more info."
< server: ESF
< x-xss-protection: 0
< set-cookie: gps=1; domain=.youtube.com; expires=mon, 28-jun-2021 11:39:13 gmt; path=/; Secure; HttpOnly
< set-cookie: ysc=mpx-p60pffm; domain=.youtube.com; path=/; sector; HttpOnly; SameSite=None
< set-cookie: visitor_info1_live=i25nzhcztqa; domain=.youtube.com; expires=sat, 25-dec-2021 11:09:13 gmt; path=/;secure; httpOnly; SameSite=None
< alt-svc: h3=":443"; ma=2592000,h3-29=":443"; ma=2592000,h3-t051=":443"; MA=2592000,H3-Q050=":443"; ma=2592000, H3-Q046=":443"; ma=2592000,h3-q043=":443"; ma=2592000, quic=":443"; ma=2592000; v="46,43"
< accept-ranges: none
< vary: accept-encoding
< transfer-encoding: chunked
<
<!docType html><html style="font-size: 10px;font-family: roboto, arial, sans-serif;" lang="en" typography typoography-spacing><head><meta http-equiv="x-ua-compatible" content="ie=edge"/><script nonce="m6im/2yfcuabovhb8ZzphQ">var ytcfg={d:function(){return window.yt&&yt.config_||ytcfg.data_|||(ytcfg.data_={})}, get:function(k,o){return k in ytcfg.d()?ytcfg.d()[k]:o},set:function(){var a=arguments;if(a.length>1)ytcfg.d()[a[0]]=a[1]; else for(var k in a[0])ytcfg.d()[k]=a[0][k]}};
13. The ports opened by Alibaba Cloud servers 1081 and 8118 need to run commands to open. Open the firewall iptables. as shown in Figure 8
[root@iZ23wv7v5ggZ ~]# cat /etc/sysconfig/iptables # Generated by iptables-save v1.4.21 on mon jun 28 19:53:18 2021 *Filter :input drop[2:80] :forward accept[0:0] :output accept[247:63813] :syn-flood -[0:0] -a input -p tcp -m tcp --dport 8118 -m state --state new -j accept -a input -p tcp -m tcp --dport 1081 -m state --state new -j accept -a input -p tcp -m tcp --dport 1080 -m state --state new -j accept -a input -i lo -j accept -a input -m state --state related,established -j accept -a input -p tcp -m state --state new -m tcp --dport 22 -j accept -a input -p tcp -m state --state new -m tcp --dport 80 -j accept -a input -p tcp -m state --state new -m tcp --dport 21 -j accept -a input -p tcp -m state --state new -m tcp --dport 20000:30000 -j accept -a input -p tcp -m state --state new -m tcp --dport 443 -j accept -a input -p icmp -m icmp --icmp-type 8 -j accept commit # completed on mon jun 28 19:53:18 2021 [root@iZ23wv7v5ggZ v2ray]# iptables -i input -p tcp --dport 1081 -m state --state new -j accept [root@iZ23wv7v5ggZ v2ray]# service iptables save iptables: Saving firewall rules to /etc/sysconfig/iptables:[ OK ] [root@iZ23wv7v5ggZ v2ray]# cat /etc/sysconfig/iptables # Generated by iptables-save v1.4.21 on Fri Jun 25 17:19:08 2021 *Filter :input drop[2:80] :forward accept[0:0] :output accept[580:261280] :syn-flood -[0:0] -a input -p tcp -m tcp --dport 1081 -m state --state new -j accept -a input -p tcp -m tcp --dport 1080 -m state --state new -j accept -a input -i lo -j accept -a input -m state --state related,established -j accept -a input -p tcp -m state --state new -m tcp --dport 22 -j accept -a input -p tcp -m state --state new -m tcp --dport 80 -j accept -a input -p tcp -m state --state new -m tcp --dport 21 -j accept -a input -p tcp -m state --state new -m tcp --dport 20000:30000 -j accept -a input -p tcp -m state --state new -m tcp --dport 443 -j accept -a input -p icmp -m icmp --icmp-type 8 -j accept commit # Completed on Fri Jun 25 17:19:08 2021 [root@iZ23wv7v5ggZ v2ray]#
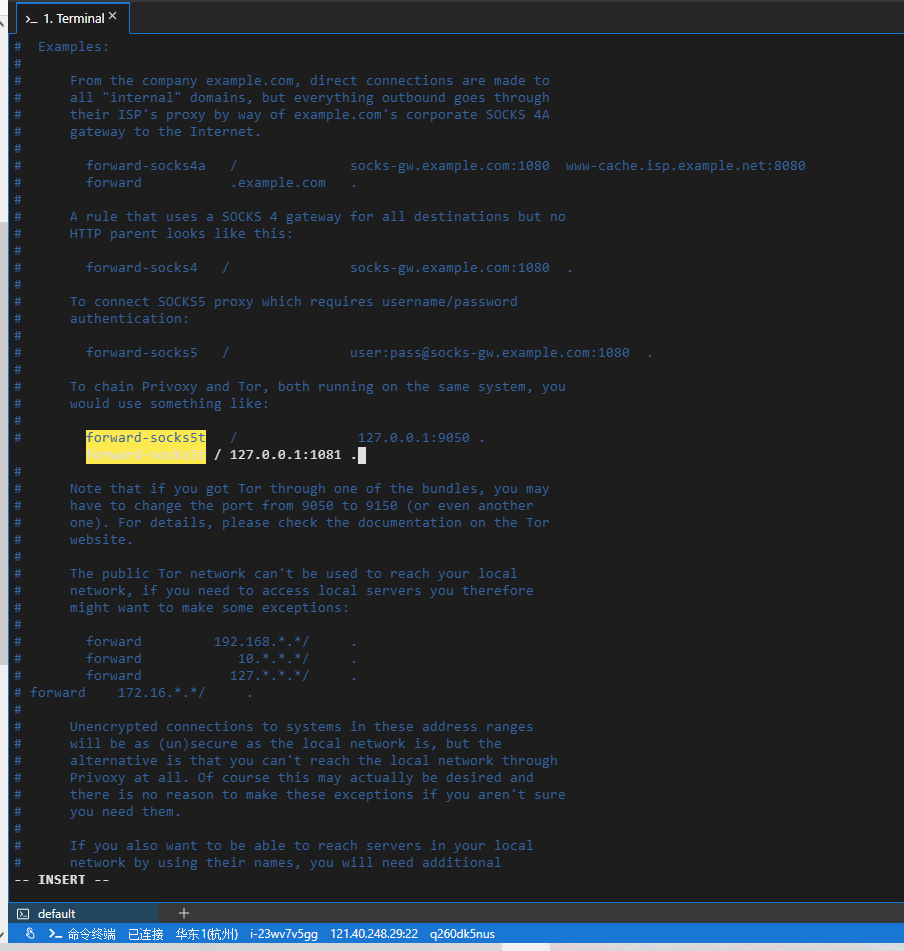
14. Install and configure Privoxy, and modify the configuration file /etc/privoxy/config. as shown in Figure 9
/usr/local/bin/v2ray -test -config /usr/local/etc/v2ray/config.json [root@iZ23wv7v5ggZ ~]# yum -y install privacy loaded plugins: fastestmirror Determining Fastest Mirrors BASE | 3.6 KB 00:00 EPEL | 4.7 KB 00:00 Extras | 2.9 KB 00:00 Updates | 2.9 KB 00:00 (1/7): base/7/x86_64/group_gz | 153 KB 00:00 (2/7): EPEL/X86_64/GROUP_GZ | 96 KB 00:00 (3/7): EPEL/X86_64/UpdateInfo | 1.0 MB 00:00 (4/7): Extras/7/x86_64/primary_db | 242 KB 00:00 (5/7): base/7/x86_64/primary_db | 6.1 MB 00:00 (6/7): EPEL/X86_64/Primary_DB | 6.9 MB 00:00 (7/7): updates/7/x86_64/primary_db | 8.8 MB 00:00 Resolving Dependencies --> running transaction check ---> Package Privoxy.x86_64 0:3.0.32-1.el7 will be installed --> finished dependency resolution Dependencies resolved ==================================== ==================================== Package arch version repository size ==================================== ==================================== installing: Privoxy x86_64 3.0.32-1.el7 EPEL 998 K transaction summary ==================================== ==================================== install 1 package Total Download Size: 998 K Installed size: 3.1 m Downloading packages: Privoxy-3.0.32-1.el7.x86_64.rpm | 998 KB 00:00 running transaction check running transaction test transaction test successfully running transaction Installing : Privoxy-3.0.32-1.el7.x86_64 1/1 Verifying : Privoxy-3.0.32-1.el7.x86_64 1/1 Installed: Privoxy.x86_64 0:3.0.32-1.el7 complete! [root@iZ23wv7v5ggZ ~]# systemctl enable privacy created symlink from /etc/systemd/system/multi-user.target.wants/privoxy.service to /usr/lib/systemd/system/privoxy.service. [root@iZ23wv7v5ggZ ~]# systemctl start Privoxy [root@iZ23wv7v5ggZ ~]# systemctl status ● Privoxy.Service - Privoxy Web Proxy with Advanced Filtering Capabilities loaded: loaded (/usr/lib/systemd/system/privoxy.service; enabled; vendor preset: disabled) Active: active (running) since thu 2021-06-24 11:08:07 CST; 5s ago process: 6845 execStart=/usr/sbin/privoxy --pidfile/run/privoxy.pid --user Privoxy /etc/privoxy/config (code=exited, status=0/success) Main PID: 6846 (Privoxy) cgroup: /system.slice/privoxy.service └─6846 /usr/sbin/privoxy --pidfile /run/privoxy.pid --user Privoxy... Jun 24 11:08:06 IZ23WV7V5GGZ systemd[1]: Starting Privoxy Web Proxy with Adv.... Jun 24 11:08:07 IZ23WV7V5GGZ systemd[1]: Started Privoxy Web Proxy with Adva.... Hint: Some lines were ellipsized, use -l to show in full. [root@iZ23wv7v5ggZ ~]# yum install w3m -y loaded plugins: fastestmirror Loading mirror speeds from cached hostfile Resolving Dependencies --> running transaction check ---> package w3m.x86_64 0:0.5.3-50.git20210102.el7 will be installed --> processing dependency: libcrypto.so.1.1(openssl_1_1_0)(64bit) for package: w3m-0.5.3-50.git20210102.el7.x86_64 --> processing dependency: libssl.so.1.1(openssl_1_1_0)(64bit) for package: w3m-0.5.3-50.git20210102.el7.x86_64 --> processing dependency: perl(nkf) for package: w3m-0.5.3-50.git20210102.el7.x86_64 --> processing dependency: libcrypto.so.1.1()(64bit) for package: w3m-0.5.3-50.git20210102.el7.x86_64 --> processing dependency: libgc.so.1()(64bit) for package: w3m-0.5.3-50.git20210102.el7.x86_64 --> processing dependency: libssl.so.1.1()(64bit) for package: w3m-0.5.3-50.git20210102.el7.x86_64 --> running transaction check ---> package gc.x86_64 0:7.2d-7.el7 will be installed ---> package openssl1-libs.x86_64 1:1.1.1g-3.el7 will be installed ---> package perl-nkf.x86_64 1:2.1.3-5.el7 will be installed --> finished dependency resolution Dependencies resolved ==================================== ==================================== Package arch version repository Size ==================================== ==================================== installing: W3M x86_64 0.5.3-50.git20210102.el7 EPEL 980 K Installing for dependencies: GC x86_64 7.2D-7.EL7 Base 158 K OpenSSL11-libs x86_64 1:1.1.1g-3.el7 EPEL 1.5 M Perl-NKF x86_64 1:2.1.3-5.EL7 EPEL 131 K transaction summary ==================================== ==================================== install 1 package (+3 dependence packages) Total download size: 2.7 m Installed size: 6.5 m Downloading packages: (1/4): GC-7.2D-7.EL7.x86_64.rpm | 158 KB 00:00 (2/4): Perl-NKF-2.1.3-5.el7.x86_64.rpm | 131 KB 00:00 (3/4): openssl1-libs-1.1.1g-3.el7.x86_64.rpm | 1.5 MB 00:00 (4/4): w3m-0.5.3-50.git20210102.el7.x86_64.rpm | 980 KB 00:00 --------------------------------------------------------------------- Total 5.0 MB/s | 2.7 MB 00:00 running transaction check running transaction test transaction test successfully running transaction installing : 1:openssl11-libs-1.1.1g-3.el7.x86_64 1/4 Installing : GC-7.2D-7.EL7.x86_64 2/4 Installing : 1:Perl-NKF-2.1.3-5.el7.x86_64 3/4 Installing : w3m-0.5.3-50.git20210102.el7.x86_64 4/4 verifying : 1:Perl-NKF-2.1.3-5.el7.x86_64 1/4 Verifying : GC-7.2D-7.EL7.x86_64 2/4 verifying : w3m-0.5.3-50.git20210102.el7.x86_64 3/4 verifying : 1: openssl11-libs-1.1g-3.el7.x86_64 4/4 Installed: w3m.x86_64 0:0.5.3-50.git20210102.el7 dependency installed: gc.x86_64 0:7.2d-7.el7 openssl11-libs.x86_64 1:1.1.1g-3.el7 perl-nkf.x86_64 1:2.1.3-5.el7 complete! [root@iZ23wv7v5ggZ ~]# vi /etc/privoxy/config [root@iZ23wv7v5ggZ ~]#
listen-address 127.0.0.1:8118 forward-socks5t / 127.0.0.1:1081 .
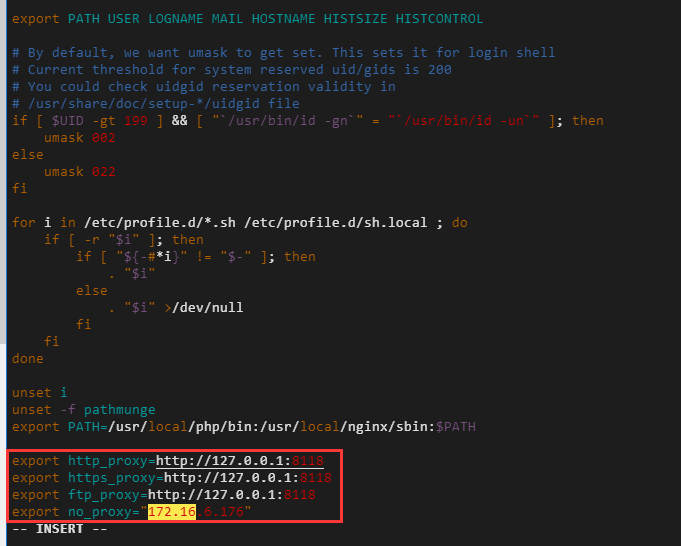
15. Set the http/https proxy, and modify the configuration file /etc/profile. 172.16.6.176 is the IP of the server intranet, indicating that there is no proxy. As shown in Figure 10
[root@iZ23wv7v5ggZ ~]# vi /etc/profile [root@iZ23wv7v5ggZ ~]# systemctl stop privoxy [root@iZ23wv7v5ggZ ~]# systemctl start Privoxy [root@iZ23wv7v5ggZ ~]# systemctl status ● Privoxy.Service - Privoxy Web Proxy with Advanced Filtering Capabilities loaded: loaded (/usr/lib/systemd/system/privoxy.service; enabled; vendor preset: disabled) Active: active (running) since fri 2021-06-25 19:17:34 cst; 10s ago process: 10823 execstart=/usr/sbin/privoxy --pidfile/run/privoxy.pid --user Privoxy /etc/privoxy/config (code=exited, status=0/success) Main PID: 10824 (Privoxy) cgroup: /system.slice/privoxy.service └─10824 /usr/sbin/privoxy --pidfile/run/privoxy.pid --user privoxy /etc/privoxy/config Jun 25 19:17:33 IZ23WV7V5GGZ systemd[1]: Starting Privoxy Web Proxy with Advanced Filtering Capabilities... Jun 25 19:17:34 IZ23WV7V5GGZ systemd[1]: Started Privoxy Web Proxy with Advanced Filtering Capabilities. [root@iZ23wv7v5ggZ ~]#
export http_proxy=http://127.0.0.1:8118 export https_proxy=http://127.0.0.1:8118 export ftp_proxy=http://127.0.0.1:8118 export no_proxy="172.16.6.176"
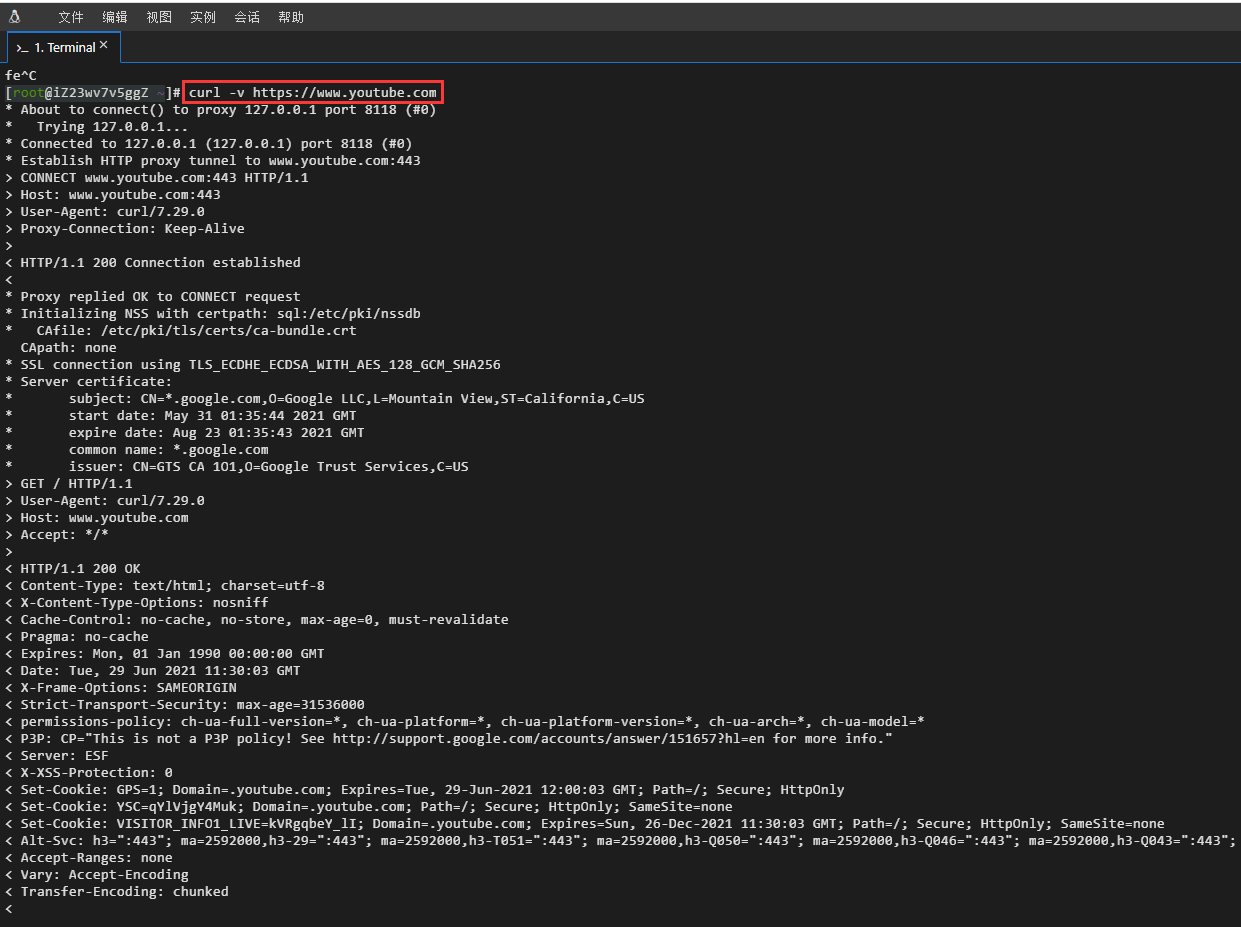
16. Test the Alibaba Cloud server based on CURL HTTP requests http://httpbin.org/ip, https://www.google.com, https://www.youtube.com. The connection was successful. as shown in Figure 11
[root@iZ23wv7v5ggZ ~]# curl -v http://httpbin.org/IP
* about to connect() to proxy 127.0.0.1 port 8118 (#0)
* Trying 127.0.0.1...
* Connected to 127.0.0.1 (127.0.0.1) Port 8118 (#0)
> Get http://httpbin.org/IP http/1.1
> user-agent: curl/7.29.0
> host: httpbin.org
> accept: */*
> proxy-connection: keep-alive
>
< http/1.1 200 OK
< date: tue, 29 Jun 2021 11:28:55 GMT
< content-type: application/json
< content-length: 31
< connection: keep-alive
< server: gunicorn/19.9.0
< access-control-allow-origin: *
< access-control-allow-credentials: true
< proxy-connection: keep-alive
<
{
"origin": "14.192.49.13"
}
* Connection #0 to Host 127.0.0.1 Left Intact
[root@iZ23wv7v5ggZ ~]# curl -v http://www.google.com
* about to connect() to proxy 127.0.0.1 port 8118 (#0)
* Trying 127.0.0.1...
* Connected to 127.0.0.1 (127.0.0.1) Port 8118 (#0)
>get http://www.google.com/http/1.1
> user-agent: curl/7.29.0
> host: www.google.com
> accept: */*
> proxy-connection: keep-alive
>
<http/1.1 302 found
< location: http://www.google.com.hk/url?sa=p&hl=en&pref=hkredirect&pval=yes&q= http://www.google.com.hk/&ust=162496617 8742441&usg=aovvaw2qc6lusz__xy4cv4128vdo
< cache-control: private
< content-type: text/html; charset=utf-8
< p3p: cp="this is not a p3p policy! see g.co/p3phelp for more info."
< date: tue, 29 Jun 2021 11:29:08 GMT
< server: GWS
< content-length: 370
< x-xss-protection: 0
< x-frame-options: SameOrigin
< set-cookie: 1p_jar=2021-06-29-11; expires=thu, 29-jul-2021 11:29:08 gmt; path=/; domain=.google.com; secure
< set-cookie: NID=218=MAQ-WWAOOHTHEWGLGFX6UC1OS1THML90KHJAA cvgj_9ogj73i3svn6kwgb4ahrx3uzh5sw0__q-y5ahjta vjtitgntahkmj_d4esuipceyijcrsskk88mu_sf6xopwh vpqqdy3zs5zdscnbvbvb5z0n0ivnrtgayv2is44z8phc; expires=wed, 29-dec-2021 11:29:08 gmt; path=/; domain=.google.com; httpOnly
< proxy-connection: keep-alive
<
<html><head><meta http-equiv="content-type" content="text/html;charset=utf-8">
<title>302 moved</title></head><body>
<h1>302 moved</h1>
The document has moved
<a href="http://www.google.com.hk/url?sa=p&amp;hl=en-c n&amp;pref=hkredirect&amp;pval=yes&amp;q=htt p://www.google.com.hk/&amp;ust=1624966178742441& AMP;USG=AOVVAW2QC6Lusz__XY4CV4128VDO">Here</a>.
</body></html>
* Connection #0 to Host 127.0.0.1 Left Intact
[root@iZ23wv7v5ggZ ~]# curl -v https://www.google.com
* about to connect() to proxy 127.0.0.1 port 8118 (#0)
* Trying 127.0.0.1...
* Connected to 127.0.0.1 (127.0.0.1) Port 8118 (#0)
* Establish HTTP Proxy Tunnel to www.google.com:443
> connect www.google.com:443 http/1.1
> host: www.google.com:443
> user-agent: curl/7.29.0
> proxy-connection: keep-alive
>
<http/1.1 200 connection established
<
* Proxy replied OK to connect request
*Initializing NSS with CertPath: SQL:/etc/pki/NSSDB
* cafile: /etc/pki/tls/certs/ca-bundle.crt
Capath: None
* SSL connection using TLS_ECDHE_ECDSA_With_AES_128_GCM_SHA256
* Server Certificate:
* subject: cn=www.google.com,o=google llc,l=mountain view,st=california,c=us
* Start Date: May 31 03:52:12 2021 GMT
* Expire Date: Aug 23 03:52:11 2021 GMT
* Common Name: www.google.com
* issuer: cn=gts ca 1o1,o=google trust services, c=us
> get/http/1.1
> user-agent: curl/7.29.0
> host: www.google.com
> accept: */*
>
<http/1.1 302 found
< location: https://www.google.com.hk/url?sa=p&hl=en&pref=hkredirect&pval=yes&q= https://www.google.com.hk/&ust=162496619 7905473&usg=AovVAW3RPXJ3M42WVO-874Ocuuaa
< cache-control: private
< content-type: text/html; charset=utf-8
< p3p: cp="this is not a p3p policy! see g.co/p3phelp for more info."
< date: tue, 29 Jun 2021 11:29:27 GMT
< server: GWS
< content-length: 372
< x-xss-protection: 0
< x-frame-options: SameOrigin
< set-cookie: 1p_jar=2021-06-29-11; expires=thu, 29-jul-2021 11:29:27 gmt; path=/; domain=.google.com; secure
< set-cookie: NID=218=OER550XI5XY2PWWVQYodouO0EO3BDFJV7WRPO ou1fmnvfwzsi9azb4-opy_cibbjn1wyt4ycjyne9ihtd ysdugidbxhzeenwst66bppphbwlppcnyqyeqis1ltdchgjw _C8xv3lslf2subti825bqgha3bam6qjvvqi2x2pj-xu; expires=wed, 29-dec-2021 11:29:27 gmt; path=/; domain=.google.com; HttpOnly
< alt-svc: h3=":443"; ma=2592000,h3-29=":443"; ma=2592000,h3-t051=":443"; MA=2592000,H3-Q050=":443"; ma=2592000, H3-Q046=":443"; ma=2592000,h3-q043=":443"; ma=2592000, quic=":443"; ma=2592000; v="46,43"
<
<html><head><meta http-equiv="content-type" content="text/html;charset=utf-8">
<title>302 moved</title></head><body>
<h1>302 moved</h1>
The document has moved
<a href="https://www.google.com.hk/url?sa=p&amp;hl=en-c n&amp;pref=hkredirect&amp;pval=yes&amp;q=htt ps://www.google.com.hk/&amp;ust=1624966197905473& ;amp;usg=aovvaw3rpxj3m42wvo-874ocuuaa">here</a>
</body></html>
* Connection #0 to Host 127.0.0.1 Left Intact
[root@iZ23wv7v5ggZ ~]# curl -v https://sitekit.withgoogle.com
* about to connect() to proxy 127.0.0.1 port 8118 (#0)
* Trying 127.0.0.1...
* Connected to 127.0.0.1 (127.0.0.1) Port 8118 (#0)
* Establish HTTP Proxy Tunnel to SiteKit.withGoogle.com:443
> connect sitekit.withgoogle.com:443 http/1.1
> host: sitekit.withgoogle.com:443
> user-agent: curl/7.29.0
> proxy-connection: keep-alive
>
<http/1.1 200 connection established
<
* Proxy replied OK to connect request
*Initializing NSS with CertPath: SQL:/etc/pki/NSSDB
* cafile: /etc/pki/tls/certs/ca-bundle.crt
Capath: None
* SSL connection using TLS_ECDHE_ECDSA_With_AES_128_GCM_SHA256
* Server Certificate:
* Subject: cn=*.appspot.com,o=Google llc,l=mountain view,st=california,c=us
* Start Date: Jun 07 01:07:29 2021 GMT
* Expire Date: Aug 30 01:07:28 2021 GMT
* Common name: *.appspot.com
* issuer: cn=gts ca 1o1,o=google trust services, c=us
> get/http/1.1
> user-agent: curl/7.29.0
> host: sitekit.withgoogle.com
> accept: */*
>
< http/1.1 200 OK
< content-type: text/html; charset=utf-8
< vary: accept-encoding
< x-cloud-trace-context: 803be8061a081faa119115967f932ca2
< date: tue, 29 Jun 2021 11:29:47 GMT
< server: Google Frontend
< content-length: 89089
< alt-svc: h3=":443"; ma=2592000,h3-29=":443"; ma=2592000,h3-t051=":443"; MA=2592000,H3-Q050=":443"; ma=2592000, H3-Q046=":443"; ma=2592000,h3-q043=":443"; ma=2592000, quic=":443"; ma=2592000; v="46,43"
<
<!doctype html>
<html lang="en-us" class="no-js glue-flexbox glue-app-ready" amp="" i-amphtml-layout="" I-AMPHTML-no-boilerplate="" transformed="self;v=1">^c
[root@iZ23wv7v5ggZ ~]# curl -v https://www.youtube.com
* about to connect() to proxy 127.0.0.1 port 8118 (#0)
* Trying 127.0.0.1...
* Connected to 127.0.0.1 (127.0.0.1) Port 8118 (#0)
* Establish HTTP Proxy Tunnel to www.youtube.com:443
> connect www.youtube.com:443 HTTP/1.1
> host: www.youtube.com:443
> user-agent: curl/7.29.0
> proxy-connection: keep-alive
>
<http/1.1 200 connection established
<
* Proxy replied OK to connect request
*Initializing NSS with CertPath: SQL:/etc/pki/NSSDB
* cafile: /etc/pki/tls/certs/ca-bundle.crt
Capath: None
* SSL connection using TLS_ECDHE_ECDSA_With_AES_128_GCM_SHA256
* Server Certificate:
* subject: cn=*.google.com,o=google llc,l=mountain view,st=california,c=us
* Start Date: May 31 01:35:44 2021 GMT
* Expire Date: Aug 23 01:35:43 2021 GMT
* Common name: *.google.com
* issuer: cn=gts ca 1o1,o=google trust services, c=us
> get/http/1.1
> user-agent: curl/7.29.0
> host: www.youtube.com
> accept: */*
>
< http/1.1 200 OK
< content-type: text/html; charset=utf-8
< x-content-type-options: nosniff
< cache-control: no-cache, no-store, max-age=0, must-revalidate
< pragma: no-cache
< Expires: Mon, 01 Jan 1990 00:00:00 GMT
< date: tue, 29 Jun 2021 11:30:03 GMT
< x-frame-options: SameOrigin
< strict-transport-security: max-age=31536000
< permissions-policy: ch-ua-full-version=*, ch-ua-platform=*, ch-ua-platform-version=*, ch-ua-arch=*, ch-ua-model=*
< p3p: cp="this is not a p3p policy! see http://support.google.com/accounts/answer/151657?hl=en for more info."
< server: ESF
< x-xss-protection: 0
< set-cookie: gps=1; domain=.youtube.com; expires=tue, 29-jun-2021 12:00:03 gmt; path=/; Secure; HttpOnly
< set-cookie: ysc=qylvjgy4muk; domain=.youtube.com; path=/;secure; HttPonly; SameSite=None
< set-cookie: visitor_info1_live=kvrgqbey_li; domain=.youtube.com; expires=sun, 26-dec-2021 11:30:03 GMT; path=/; Secure; HttpOnly; SameSite=None
< alt-svc: h3=":443"; ma=2592000,h3-29=":443"; ma=2592000,h3-t051=":443"; MA=2592000,H3-Q050=":443"; ma=2592000, H3-Q046=":443"; ma=2592000,h3-q043=":443"; ma=2592000, quic=":443"; ma=2592000; v="46,43"
< accept-ranges: none
< vary: accept-encoding
< transfer-encoding: chunked
<
<!doctype html>^c
[root@iZ23wv7v5ggZ ~]#